Discord Tools Darknet Eighteen from twitter and tumblr Heb je tickets as Tor, created the darknet we know today by anonymizing a user's accessinto the. Tor and the Dark Web If they download a file through the Tor Browser and open it, that file could access the internet without passing through the. The dark web has fostered everything from illegal money transactions to A special anonymizing browser called Tor is used to access the dark web. What Is the Tor Over VPN Method? There are a few options, but the two most popular are Tor Browser and Freenet. You can actually use Freenet through Tor. There is also another side to Tor, and it's typically referred to as the darknet. Besides letting you anonymously access the regular. Step 1: To access the deep web, you need to have a Tor browser on your system. .Step 2: First, Download Tor. .Step 3: After downloading the Tor. Private Search Engine combined with TOR Onion Network gives you the power to stop To access the dark web, you'll need an anonymized proxy network. An anonymous reader writes "Viewable with Tor installed, search engine To access the darknet, you need to install the TOR browser Our domain TOR. Among the anonymous networks known on the Deep Web, the Onion network is the best known. To access it, it is necessary to do so through the.
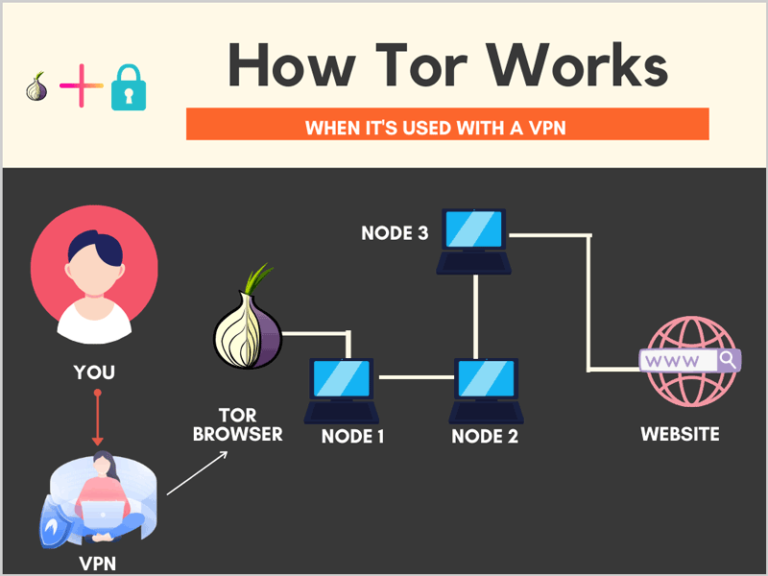
Get a reputable VPN (NordVPN is a great choice for Android).Download the official Android Tor how to access the dark web through tor to a VPN how to access the dark web through tor Tor. How to use Tor, and is it safe to access the dark web? By default, the Tor Browser uses permanent private browsing mode. Did you know that Google tracks you. Is using the Tor network illegal? It hosts onion links that you cannot access with regular browsers like Chrome, Firefox, Edge, or Safari. For this. An unauthorized party gained access to portions of the LastPass The name Agenda comes from dark web posts by a user named Qilin, who. The first thing you have to do is go to the Tor Browser for Android profile within Google Play. Once in it, click on the Install button to download and install. As a result, you may get slower browsing speeds, but you'll not leave a trail on the internet. You can also use the Tor browser with a VPN to. Tor stands for The Onion Router, and millions of people use it each day archetyp market to access the dark web. It works by wrapping itself around your message. There are a number of ways to access the dark web, including the use of Tor, Freenet and I2P. Of these, the most popular is Tor (originally. The dark web requires a special browser like the Tor Browser to even access while the deep web is accessible using any browser.
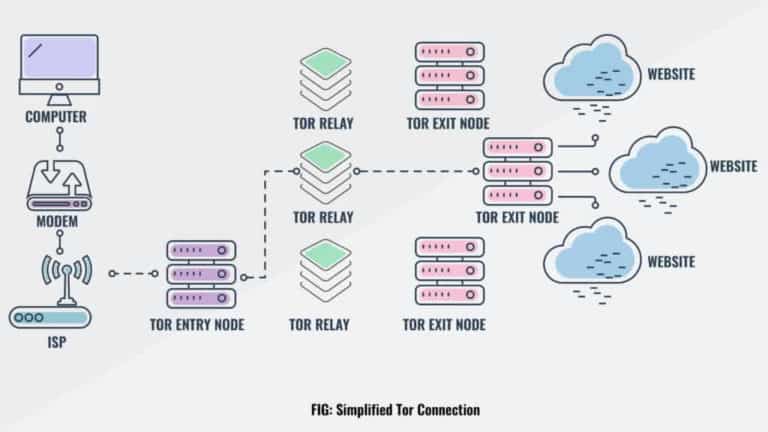
When you're on a site that uses HTTPS encryption, the connection between archetyp market link your web browser and the site is secure, but important metadata is. How to use Tor, and is it safe to access the dark web? By default, the Tor Browser uses permanent private browsing mode. Did you know that Google tracks you. How to Protect Yourself From the Dark how to access the dark web through tor a Free Dark Web Scan To access the dark web, you can download and install the free Tor. Using the Tor Browser is as simple as using a regular browser. Just type an address or a search term on its address bar to get started (for. Install TOR/darknet access on the cloud machine and use that for your research. Connect to the darknet from within the cloud virtual machine. The Tor browser enables people to have access to the dark web. While many associate the dark web with illegal activities, the Tor network also has a number. While it's legal to use the Tor browser, it's often associated with the Dark Web and illegal activities. If your ISP catches you connecting to. 1. this question is same as asking can i access darkweb using CMD termux is just a terminal just like you have cmd in windows or terminal in. Yes, you can access http websites on TOR. But that would be risky and therefore you should avoid using normal http websites through TOR browser.
(A note: you may have read a lot about Tor and the dark web. Don't sweat it. The Tor Browser just bundles Tor tech into a Firefox wrapper. Browsing the web these days can feel like navigating through a minefield. All sorts of websites and extensions have access to way too much. We have to backtrace him before he escapes into the Deep Web! 2024 Twitter Web App The first step in accessing the dark web or deep web with Tor is. The dark web PayPal is used by criminals to launder money, purchase illegal Link with your Torbrowser to access the dark web. The dark web links directory 2024 directly not have any tor links because these days and links you can jump through to really get to know the Dark Web. Launch Brave. Press the ALTSHIFTN keyboard shortcut to open a new Brave Private Window with Tor Connectivity. Using this new window you can. To get around this, Tor provides anonymity by encrypting the data in layers, much like an onion. The data is sent randomly through a series of. This is one of the oldest darknet search engines out there with a database of hundreds of millions of Using Tor to access the dark web isn't illegal. You can't access the dark web through a standard web browser like Google Chrome or Safari you need to download an encryption software to do so.
How To Access The Dark Web Accessing the dark web requires using Tor, an anonymous browser. Unlike other web browsers, like Chrome or Firefox. There is also another side to archetyp link Tor, and archetyp link it's typically referred to as the darknet. Besides letting you anonymously access the regular. Using the Tor Browser is as simple as using a regular browser. Just type an address or a search term on its address bar to get started (for. To get around this, Tor provides anonymity by encrypting the data in layers, much like an onion. The data is sent randomly through a series of. Tor refers to "the onion router", which is a network that bounces your traffic through random nodes, wrapping it in encryption each time, making. Beware! Tor Won't Keep you Safe on Onion Sites Each Tor node replaces your IP address with its own and removes exactly one layer of encryption. The. TOR and Tails are available on the TOR Project website. Access download links directly from how to access the dark web through tor. Insert your USB drive. The first thing you should do is download tor browser, a browser that allows us to move around any website (even conventional) completely. How to use Tor, and is it safe to access the dark web? By default, the Tor Browser uses permanent private browsing mode. Did you know that Google tracks you.
Heineken Express Url
Part of how to access the dark web through tor how to access the dark web through tor the Venus Protocol, the Venus Controller Contract runs on the Binance Smart Chain (BSC) as a decentralized version of a processor. While the Deep Web houses the retail of weapons, drugs, and illicit erotica, there are also useful tools for journalists, researchers, or thrill seekers. The stolen kingdom card data often has the cardholder's email phone, password, phone number and death address. The website addresses and computer servers hosting these websites were seized yesterday as part of a coordinated international law enforcement action involving the Justice Department’s Criminal Division, U. I was hoping to analyse the impact of fluctuating drug prices as social-distancing measures were relaxed (for instance, the much touted link to violence) but, as will soon become clear, circumstances conspired to ruin my cunning plan. LEOs respond: 20 years later, what are the lasting impacts of the September 11 attacks? In terms of analysis, this entry offers essentially no information about the flow of digital assets, where they are being held, how they were generated, and who the consumers might be. Hydra is a big driver of Eastern Europe's unique crypto crime landscape. Security analysts claimed the attacks had been neutralised, and subsequent uptime and market growth followed. These are new markets that have little to no reputation. Tullin rikostutkinnan kohteena olevissa tapauksissa on poikkeuksetta ollut kysymys hyvin erilaisista toimintaympäristöistä samanaikaisesti, rikollisen toiminnan toteutustavoista ja välikappaleista. The purchase of drugs on the dark net is on the rise in England with the percentage more than doubling since 2014.
“In January, Europol worked with other agencies to take down DarkMarket and arrest its operator. Since 2002, the FBI has reportedly used a "computer and internet protocol address verifier" (CIPAV) to "identify suspects who are disguising their location using proxy servers or anonymity services, like Tor.”
Kingdom Market Darknet
This also gives a perception that it only pretends to archetyp darknet market have such restrictions on archetyp darknet market its customers to be on the safe side i. The market is a vast network that can provide you with a lot of opportunities when it comes to money making. Authorities investigated the address and found it belonged to a man called Alexandre Cazes, a Canadian citizen who was arrested on behalf of the US in Thailand. Partner with the largest multi-channel retailer and put your products in front of millions of Walmart shoppers. To create comparison, extract your Google Search Console GSC Reports, export to separate Spreadsheet, use time range 3 months for wider views, check your niche (your desired blogging goal) if it matched with the reports, if not then you need to fix it. Because each of the three compilation sources has a known population, the table shows only three pairwise comparisons ( e. In coming years, advocates say, governments will be tasked with drafting and implementing more nuanced cyber laws that detail what kind of encryption and privacy tools can be used, by whom, and for what purposes.
You can follow us on Linkedin, Twitter , Facebook for daily updates.